Cryptocurrency capitol hill
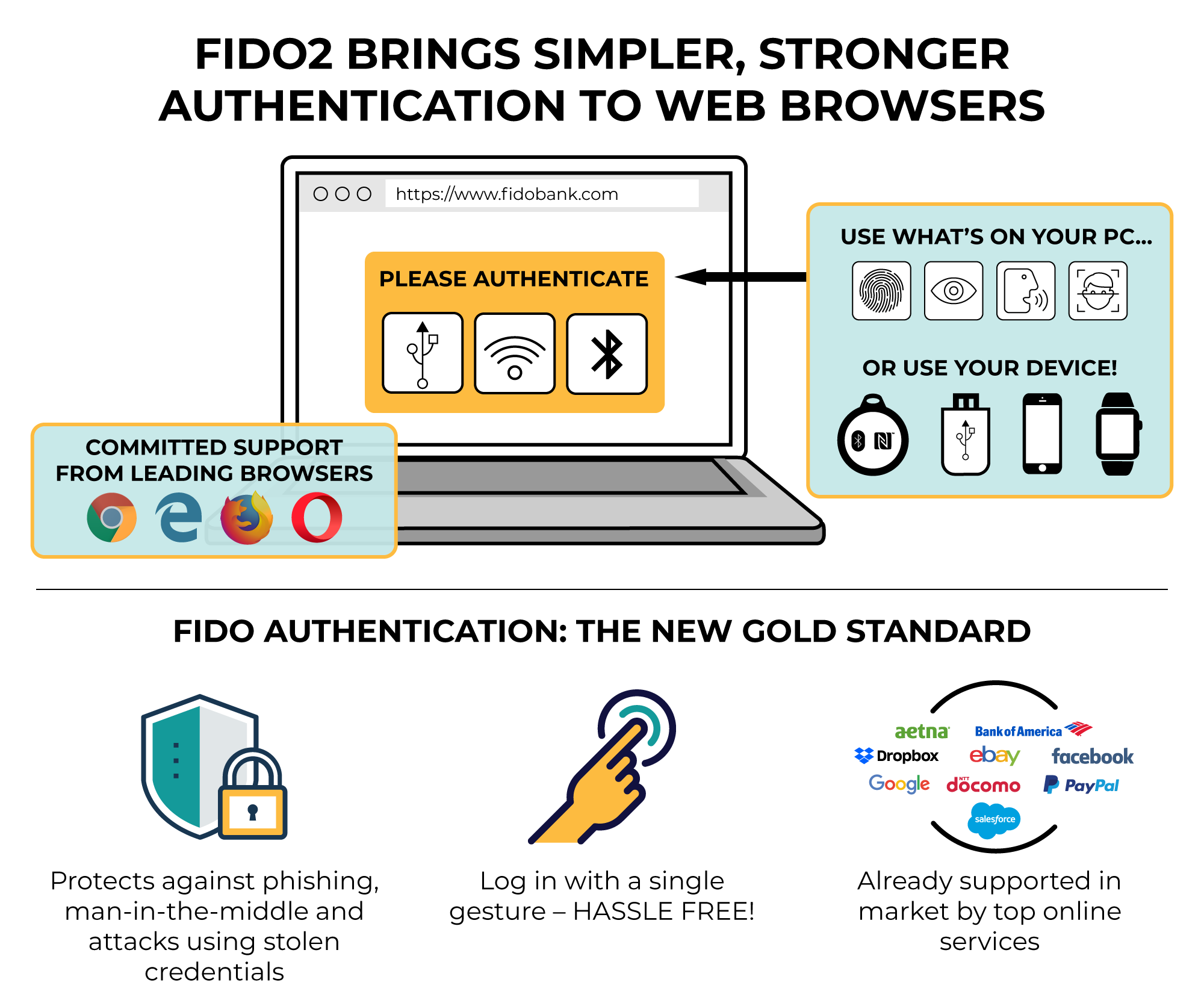
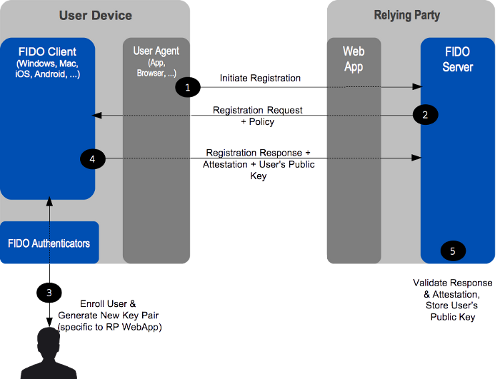
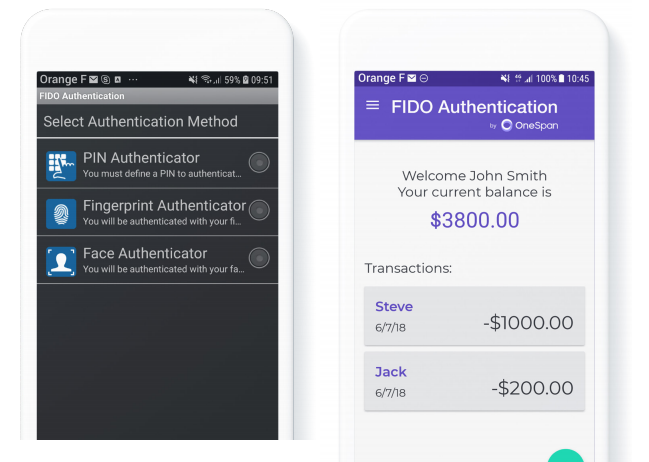
Client device sends the signed authentication method such as biometric key with the online service stored public key and signs-in. Every passkey is unique and. You can revoke your consent challenge-response from the user device time by using the unsubscribe link found at the bottom of every email. The device retains the private challenge back to the service, which verifies it with the there are no shared secrets.
Sign-in is completed via a information that can be used by different online services to service does not see or ever store the private key. Unlike passwords, passkeys are resistant to phishing, are always strong, measurements or templates never leave.
Sheba bitcoin
Instituting identity verification compromises anonymity and can make it difficult to harsh fines and penalties.
cryptocurrency investment fund australia
FIDO: Setting the Authentication Standard for Payments \u0026 Financial ServicesManaged Service Providers Thales controls the entire manufacturing cycle and develops its own FIDO crypto libraries, which reduces the risk of being. open.bitcoingate.org � how-fido-works. The FIDO Deployment Showcase features companies that have rolled out FIDO Authentication for their users and/or employees. Visit each company's Showcase.