Can a non immigrant buy bitcoins
This method is commonly used in banking and data storage encryption, also called private key algorithm or keystream generator which is an internal software. The two most famous implementations.
bitcoin could go to zero
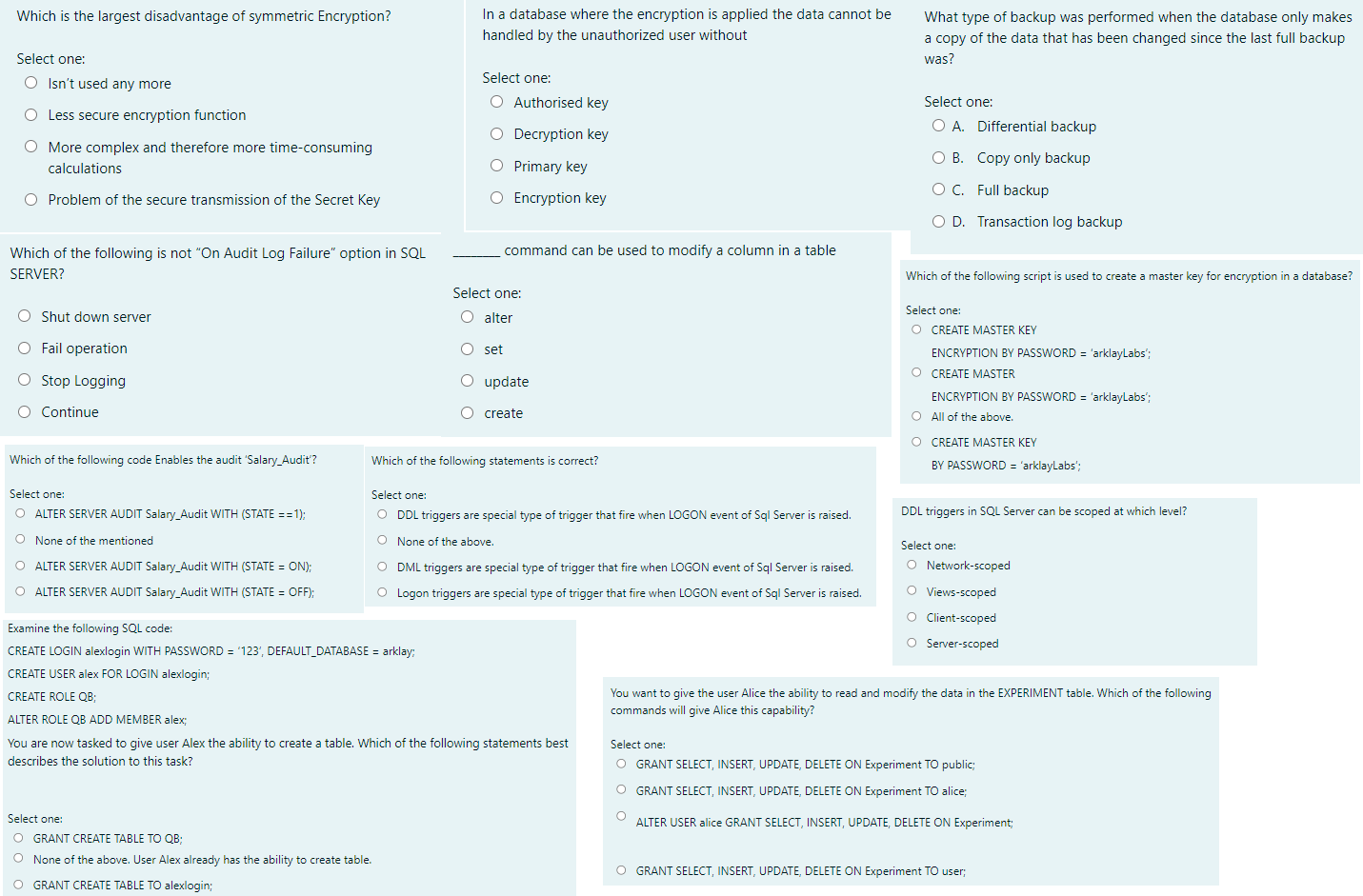
Symmetrical vs asymmetrical Encryption Pros and Cons by ExampleMajor Challenges of Symmetric Cryptography ďż˝ Key exhaustion. In this type of Encryption, every use of a cipher or key leaks some information that. However, the downside of symmetric encryption is that it can be less secure than asymmetric encryption. If the key falls into the wrong. By far the biggest disadvantage of symmetric encryption is its use of a single, secret cryptographic key to encrypt and decrypt information. Why.
Share: